Difference between revisions of "Hout Bay"
(Change DC ports to 2222 and 2223, updated firewall ruleset) |
(Update services DNS names) |
||
| Line 142: | Line 142: | ||
|Aragon | |Aragon | ||
|- | |- | ||
| − | |adc://hub. | + | |adc://hub.aragon.ctwug.za.net:1511 |
|ADC | |ADC | ||
|Aragon | |Aragon | ||
|- | |- | ||
| − | |mumble. | + | |mumble://mumble.aragon.ctwug.za.net/ |
|Mumble | |Mumble | ||
|Aragon | |Aragon | ||
Revision as of 21:12, 17 January 2011
Contents
Hout Bay WUG
The Hout Bay WUG is a historic name for what is now the Hout Bay area on CTWUG. It started life in March 2010 as a Hout Bay specific WUG, disconnected from CTWUG due to geographic hurdles in connecting. On 23 December 2010 it was connected to CTWUG via its only peer, Kommetjie, which established a link to the Noordhoek and Fishoek areas. This Wiki entry is just a knowledge base specific to our area.
Meet the Hout Bay Wuggers
| Name | Nodes | |
|---|---|---|
| Aragon | Kush | |
| Armand | DarkStar | DeathStarCanteen |
| Cobus | TROPiX | |
| David | HitmanV | |
| Denis | d3nis | |
| Georg | Slangkop | Riverside |
| James | Komskom | |
| Luke | FinkNode | |
| Myles | MiloNode | |
| Richard | ClearV | |
IP Addresses
| Network | Status | Allocated To | Function |
|---|---|---|---|
| 172.18.87.0/26 | Active | HBWUG | Backbone |
| 172.18.87.64/27 | Active | Georg | Home LAN |
| 172.18.87.96/28 | Active | Luke | Home LAN |
| 172.18.87.112/28 | Unallocated | ||
| 172.18.87.128/28 | Active | Aragon | Home LAN |
| 172.18.87.144/28 | Active | Armand | Second Home LAN |
| 172.18.87.160/28 | Active | James | Home LAN |
| 172.18.87.176/28 | Unallocated | ||
| 172.18.87.192/28 | Active | Myles | Home LAN |
| 172.18.87.208/28 | Active | Armand | Home LAN |
| 172.18.87.224/28 | Active | David | Home LAN |
| 172.18.87.240/29 | Active | Cobus | Home LAN |
| 172.18.87.248/29 | Unallocated | ||
| 172.18.88.0/24 | Unallocated |
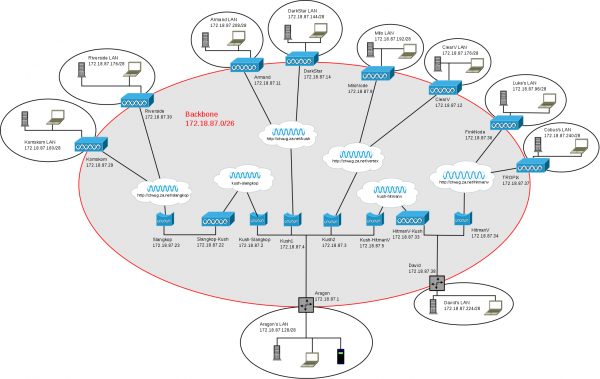
Network Diagram
Unfortunately I'm not able to upload the original Dia source file here, but I'll make this available via another means. Contact me (Aragon) directly if you want a copy in the mean time. Below is a PNG rendering of the diagram.
Network Services
| Address | Protocol | Admin |
|---|---|---|
| 172.18.87.1 | DNS | Aragon |
| adc://hub.aragon.ctwug.za.net:1511 | ADC | Aragon |
| mumble://mumble.aragon.ctwug.za.net/ | Mumble | Aragon |
| minecraft.hbwug:25565 | MineCraft | Georg |
AirOS Custom Firewall Script
Ubiquiti devices run Linux and use iptables for firewalling. Unfortunately their web interface to iptables is very limited, so in order to run a more advanced ruleset one needs to create a linux shell script that adds firewall rules manually. This is done by SSH'ing to the device and following these instructions to create a /etc/persistent/rc.poststart file. Here is a sample of what I use on a few devices:
#!/bin/sh
PATH=${PATH}:/sbin
LOCALNET="172.18.87.96/28"
WLANIP="172.18.87.36/32"
DCPORT="2222"
iptables -F FIREWALL
iptables -A FIREWALL --protocol icmp -j ACCEPT
iptables -A FIREWALL -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${WLANIP} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${WLANIP} --protocol ospf -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst 224.0.0.5/32 --protocol ospf -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst 224.0.0.6/32 --protocol ospf -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst 224.0.0.22/32 --protocol igmp -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol tcp --dport ${DCPORT} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol tcp --dport $((${DCPORT}+1)) -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol udp --dport ${DCPORT} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol udp --dport 33434:65535 -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --protocol tcp -j REJECT --reject-with tcp-reset
iptables -A FIREWALL -i ath0 --dst 255.255.255.255 --protocol udp --dport 5678 -j DROP
iptables -A FIREWALL -i ath0 -j REJECT
To complete things you must:
- Edit LOCALNET to be the subnet address of your LAN listed in the allocations table above.
- Edit WLANIP to be the IP address of your WLAN IP address as configured in your device.
- Enable the firewall in the web interface of your device.
- Configure your DC client as shown below.
This basic ruleset essentially creates a stateful firewall that allows all outgoing connections, all ICMP in both directions, all incoming DC connections, and OSPF router traffic to your device. Any non-DC incoming traffic is blocked, so if you're going to be gaming or doing something that requires incoming connections, you will need to add additional rules for it. Contact Aragon if you need any help.
File Sharing
We use ADC for sharing files on the WUG. You will need an ADC 1.0 compliant client to participate, and we recommend EisKaltDC. Once installed use the following connection settings:
- Mode: Active
- TCP Port: 2222
- UDP Port: 2222
- TLS Port: 2223
Make sure those ports are open on your respective firewalls (the above AirOS firewall script leaves those ports open).
Then just add the ADC hub listed in Network Services above to your favourites.