Difference between revisions of "Hout Bay"
(Add Denis, IP cleanup) |
|||
| Line 29: | Line 29: | ||
|[http://wind.ctwug.za.net/wind/?page=nodes&node=1767 HitmanV] | |[http://wind.ctwug.za.net/wind/?page=nodes&node=1767 HitmanV] | ||
|[http://wind.ctwug.za.net/wind/?page=nodes&node=2813 Spike] | |[http://wind.ctwug.za.net/wind/?page=nodes&node=2813 Spike] | ||
| + | |- | ||
| + | |Denis | ||
| + | |d3nis | ||
| + | |colspan="2"|[http://wind.ctwug.za.net/wind/?page=nodes&node=2187 d3nis] | ||
|- | |- | ||
|Georg | |Georg | ||
| Line 75: | Line 79: | ||
|Backbone | |Backbone | ||
|- | |- | ||
| − | |172.18.87.64/ | + | |172.18.87.64/26 |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
|Unallocated | |Unallocated | ||
| | | | ||
| Line 155: | Line 149: | ||
|Home LAN | |Home LAN | ||
|- | |- | ||
| − | |172.18.102.144/ | + | |172.18.102.144/29 |
| + | |Active | ||
| + | |Denis | ||
| + | |Home LAN | ||
| + | |- | ||
| + | |172.18.102.152/29 | ||
|Unallocated | |Unallocated | ||
| | | | ||
| Line 260: | Line 259: | ||
|Mumble | |Mumble | ||
|Aragon | |Aragon | ||
| − | |||
| − | |||
| − | |||
| − | |||
|} | |} | ||
Revision as of 23:18, 30 April 2011
Contents
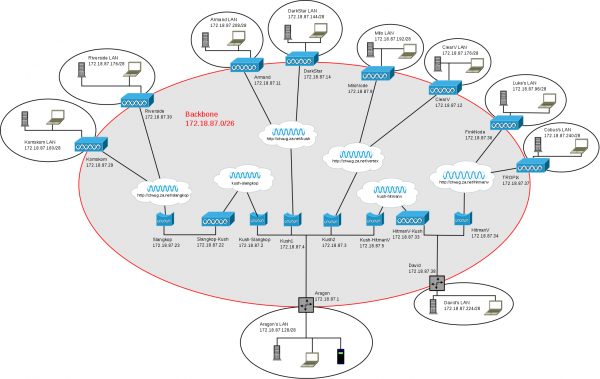
Hout Bay WUG
The Hout Bay WUG is a historic name for what is now the Hout Bay area on CTWUG. It started life in March 2010 as a Hout Bay specific WUG, disconnected from CTWUG due to geographic hurdles in connecting. On 23 December 2010 it was connected to CTWUG via Kommetjie, Noordhoek and Fishoek areas. This Wiki entry is just a knowledge base specific to our area.
Meet the Hout Bay Wuggers
| Name | Nick | Nodes | |
|---|---|---|---|
| Aragon | Aragon | Kush | Aragon |
| Armand | armthedark | DarkStar | DeathStarCanteen |
| Cobus | ObiCanobi | TROPiX | |
| David | HitmanV | HitmanV | Spike |
| Denis | d3nis | d3nis | |
| Georg | Georg | Slangkop | Riverside |
| James | flamer | Komskom | |
| Juan | JuanH | dizzy | |
| Luke | InHumaN | FinkNode | |
| Myles | Milo | MiloNode | |
| Richard | Richard | ClearV | |
Network Layout
IP Addresses
| Network | Status | Allocated To | Function |
|---|---|---|---|
| 172.18.87.0/26 | Active | HBWUG | Backbone |
| 172.18.87.64/26 | Unallocated | ||
| 172.18.87.128/28 | Active | Aragon | Home LAN |
| 172.18.87.144/28 | Active | Armand | Second Home LAN |
| 172.18.87.160/28 | Unallocated | ||
| 172.18.87.176/28 | Active | Richard | Home LAN |
| 172.18.87.192/29 | Active | Myles | Home LAN |
| 172.18.87.200/29 | Unallocated | ||
| 172.18.87.208/28 | Active | Armand | Home LAN |
| 172.18.87.224/28 | Active | David | Home LAN |
| 172.18.87.240/28 | Unallocated | ||
| 172.18.88.0/24 | Unallocated | ||
| 172.18.102.0/26 | Reserved | HBWUG | Backbone |
| 172.18.102.64/26 | Unallocated | ||
| 172.18.102.128/28 | Reserved | Aragon | Home LAN |
| 172.18.102.144/29 | Active | Denis | Home LAN |
| 172.18.102.152/29 | Unallocated | ||
| 172.18.102.160/28 | Reserved | David | Home LAN |
| 172.18.102.176/28 | Reserved | Richard | Home LAN |
| 172.18.102.192/28 | Active | Juan | Home LAN |
| 172.18.102.208/28 | Unallocated | ||
| 172.18.102.224/28 | Reserved | Armand | Home LAN |
| 172.18.102.240/28 | Reserved | Armand | Home LAN |
| 172.18.103.0/25 | Unallocated | ||
| 172.18.103.128/28 | Reserved | Luke | Home LAN |
| 172.18.103.144/28 | Unallocated | ||
| 172.18.103.160/29 | Active | David | Home LAN 2 |
| 172.18.103.168/29 | Unallocated | ||
| 172.18.103.176/28 | Unallocated | ||
| 172.18.103.192/29 | Reserved | Milo | Home LAN |
| 172.18.103.200/29 | Unallocated | ||
| 172.18.103.208/28 | Active | Cobus | Home LAN |
| 172.18.103.224/27 | Unallocated |
Network Services
| Address | Protocol | Admin |
|---|---|---|
| 172.18.87.1 | DNS | Aragon |
| adc://hub.aragon.ctwug.za.net:1511 | ADC | Aragon |
| mumble://mumble.aragon.ctwug.za.net | Mumble | Aragon |
File Sharing
We use ADC for sharing files on HBWUG. You will need an ADC 1.0 compliant client to participate. CTWUG's WugDC++ is compatible, but EiskaltDC is another recommended option. If using EiskaltDC, configure the connection settings as follows:
- Mode: Active
- TCP Port: 2222
- UDP Port: 2222
- TLS Port: 2223
Make sure those ports are open on your respective firewalls, especially the Windows firewall and any anti-virus firewalls.
Then just add the ADC hub listed in Network Services above to your favourites.
Ubiquiti Customisations
We use a number of Ubiquiti customisations to make things run smoother on HBWUG. The following instructions are intended for wuggers with some networking and Unix knowledge. Most of the changes below need to be done on the command line of your device via SSH.
Step 1: Load OSPF firmware
This requires custom Ubiquiti firmware. Either obtain a precompiled image from Aragon or build one yourself by following: Adding OSPF support to Ubiquiti devices.
Load the firmware to your device using the "Update" function in the web interface. Once its loaded and your device has rebooted with the new firmware, continue to the next step.
Step 2: Setup shell profile
From this point on do NOT reboot your device again until you've completed step 5.
Create /etc/persistent/profile with contents:
PS1='\[\e]1;\h-term\a\e]2;\h:\w\a\]\h\$ ' alias reload='/etc/persistent/rc.ctwug reload'
Step 3: Setup BIRD
Create a BIRD configuration script in /etc/persistent/bird4.conf.sh with contents:
mkbirdconf () {
cat >${BIRDCONF} <<_EOF
log stderr all;
router id ${ROUTERID};
filter ospfin
prefix set hbwug;
ip set hbwuggw;
{
hbwug = [ 172.18.87.0/24+, 172.18.88.0/24+, 172.18.102.0/23+ ];
hbwuggw = [ 172.18.87.0, 172.18.102.0 ];
if net ~ hbwug then {
if gw.mask(26) ~ hbwuggw then accept;
reject;
}
if net ~ 172.16.0.0/12 then accept;
reject;
}
protocol kernel {
persist;
learn;
description "kernel";
scan time 60;
import none;
export all;
}
protocol device {
scan time 60;
}
_EOF
if [ -e ${BIRDCONF}.local ]; then
cat ${BIRDCONF}.local >>${BIRDCONF}
fi
cat >>${BIRDCONF} <<"_EOF"
protocol ospf wug {
tick 1;
description "WUG";
import filter ospfin;
_EOF
case ${NETMODE} in
router)
cat >>${BIRDCONF} <<"_EOF"
export all;
area 0.0.0.0 {
interface "ath0" {
cost 10;
hello 10;
retransmit 20;
type broadcast;
authentication none;
};
interface "eth0" {
cost 10;
type broadcast;
stub;
};
};
_EOF
;;
bridge)
cat >>${BIRDCONF} <<"_EOF"
export none;
area 0.0.0.0 {
interface "br0" {
cost 10;
priority 0;
hello 10;
retransmit 20;
type broadcast;
authentication none;
};
};
_EOF
;;
esac
cat >>${BIRDCONF} <<"_EOF"
}
_EOF
}
Step 4: Create firewall script
Ubiquiti devices run Linux and use iptables for firewalling. Unfortunately Ubiquiti's web interface to iptables is very limited, so in order to run a more advanced firewall we add a custom firewall script.
Create /etc/persistent/rc.firewall with contents:
DCPORT="2222"
TORRENTPORT="7000"
iptables -F FIREWALL
iptables -A FIREWALL --protocol icmp -j ACCEPT
iptables -A FIREWALL -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${WLANIP} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${WLANIP} --protocol ospf -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst 224.0.0.5/32 --protocol ospf -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst 224.0.0.6/32 --protocol ospf -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst 224.0.0.22/32 --protocol igmp -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol tcp --dport ${DCPORT} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol tcp --dport $((${DCPORT}+1)) -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol udp --dport ${DCPORT} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol udp --dport ${TORRENTPORT} -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --dst ${LOCALNET} --protocol udp --dport 33434:65535 -m state --state NEW -j ACCEPT
iptables -A FIREWALL -i ath0 --protocol tcp -j REJECT --reject-with tcp-reset
iptables -A FIREWALL -i ath0 --dst 255.255.255.255 --protocol udp --dport 5678 -j DROP
iptables -A FIREWALL -i ath0 -j REJECT
The above is a starting point that will work for most wuggers. Modify it as you need if you understand iptables.
Also remember to:
- Enable the firewall in the web interface of your device. (after step 6)
- Configure your DC client as shown above.
Step 5: Create boot time HBWUG scripts
This step creates the necessary boot time code that allows steps 2 and 3 to work. Create the following files:
/etc/persistent/config.php:
#!/bin/cgi -q
<?
chdir("/usr/www");
include("lib/settings.inc");
$cfg = @cfg_load($cfg_file);
if ($cfg == -1) { exit; }
$netmode = cfg_get($cfg, "netmode");
$fwstatus = cfg_get($cfg, "iptables.status");
$lannet = cfg_get($cfg, "netconf.1.ip") + "/" + cfg_get($cfg, "netconf.1.netmask");
$wlanip = cfg_get($cfg, "netconf.2.ip");
$bridgeip = cfg_get($cfg, "netconf.3.ip");
echo("NETMODE=\"$netmode\"\n");
echo("FWSTATUS=\"$fwstatus\"\n");
echo("LOCALNET=\"$lannet\"\n");
echo("WLANIP=\"$wlanip\"\n");
echo("BRIDGEIP=\"$bridgeip\"\n");
?>
BIRDENABLE=1
/etc/persistent/rc.ctwug:
#!/bin/sh
eval "$(/etc/persistent/config.php)"
. /etc/persistent/bird4.conf.sh
PATH=${PATH}:/sbin
BIRDCONF=/etc/persistent/bird4.conf
FWCONF=/etc/persistent/rc.firewall
[ -z "${BIRDENABLE}" ] && BIRDENABLE=0
case "$1" in
start|reload)
STARTBIRD=0
STARTFW=0
if [ "${NETMODE}" = "router" ]; then
for f in /proc/sys/net/ipv4/conf/*; do
echo 1 >${f}/accept_redirects
echo 1 >${f}/send_redirects
done
if [ "${FWSTATUS}" = "enabled" -a -e ${FWCONF} ]; then
STARTFW=1
fi
if [ ${BIRDENABLE} -eq 1 -a -n "${WLANIP}" ]; then
ROUTERID=${WLANIP}
STARTBIRD=1
fi
elif [ "${NETMODE}" = "bridge" ]; then
if [ ${BIRDENABLE} -eq 1 -a -n "${BRIDGEIP}" ]; then
ROUTERID=${BRIDGEIP}
STARTBIRD=1
fi
fi
if [ "${1}" = "start" ]; then
echo "CTWUG starting"
else
echo "CTWUG reloading:"
fi
if [ ${STARTFW} -eq 1 ]; then
if [ "${1}" = "reload" ]; then
if [ "${2}" = "fw" -o -z "${2}" ]; then
echo " firewall"
fi
fi
. ${FWCONF}
fi
if [ ${STARTBIRD} -eq 1 ]; then
if [ "${1}" = "reload" ]; then
if [ "${2}" = "ospf" -o -z "${2}" ]; then
echo " OSPF"
/usr/bin/bird4.init stop
fi
fi
mkbirdconf
sleep 1
/usr/bin/bird4.init start
fi
;;
stop)
echo "CTWUG shutdown"
/usr/bin/bird4.init stop
;;
esac
/etc/persistent/rc.poststart:
/etc/persistent/rc.ctwug start
/etc/persistent/rc.prestop:
/etc/persistent/rc.ctwug stop
Step 6: Finishing touches
Run the following commands from within /etc/persistent:
chmod +x config.php rc.ctwug save
All done! When you reboot your router the changes you made should take effect.
Extra: Making changes
If changes need to be made to bird4.conf.sh or rc.firewall, either or both must be reloaded for the changes to take effect.
To reload the firewall ruleset:
reload fw
To reload the OSPF configuration:
reload ospf
Or to reload both:
reload
Once you've tested the changes and are happy, don't forget to save your changes:
save